I tried to get them to call it GNU Linux Essentials, but it wasn’t happening. So, full disclosure, I was brought in to edit and review the content for correctness. What a show. Most of the content they paid for from Cisco was plagiarized and on top of that, incorrect.
The “writer”, I use the term loosely had copied from various sources but the worst issue was when she reworded how the kernel number standard happens and … that was not correct at all. You cannot reword a standard or formula. I had seen this in tech docs when working at a HRIS software company also. The “writers” reword and make formulas incorrect. This is why it is so important to have a good technical writer.
Fast forward – this is still happening in tech: In one case, I was working for an AI startup in 2020, where they wanted me to edit the writing of less knowledgeable authors and I told the manager… It would be faster if I had simply written the content myself. It was garbage.
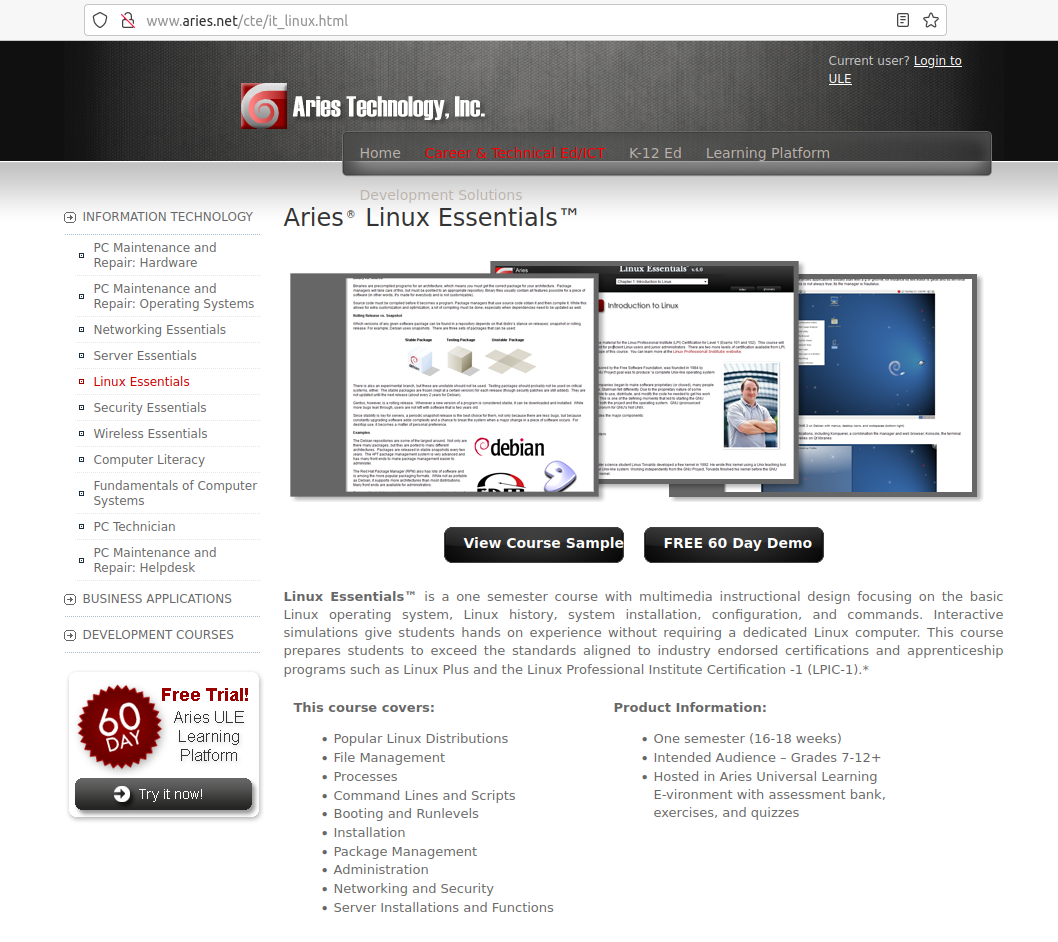
So, anyway, I wrote 13 chapters as the sole technical write for CBT used at universities worldwide, including my alma mater. While I never received promised royalties and didn’t even have my name in the book, it was an amazing start for many wanting to learn Linux and get Linux+ certification.
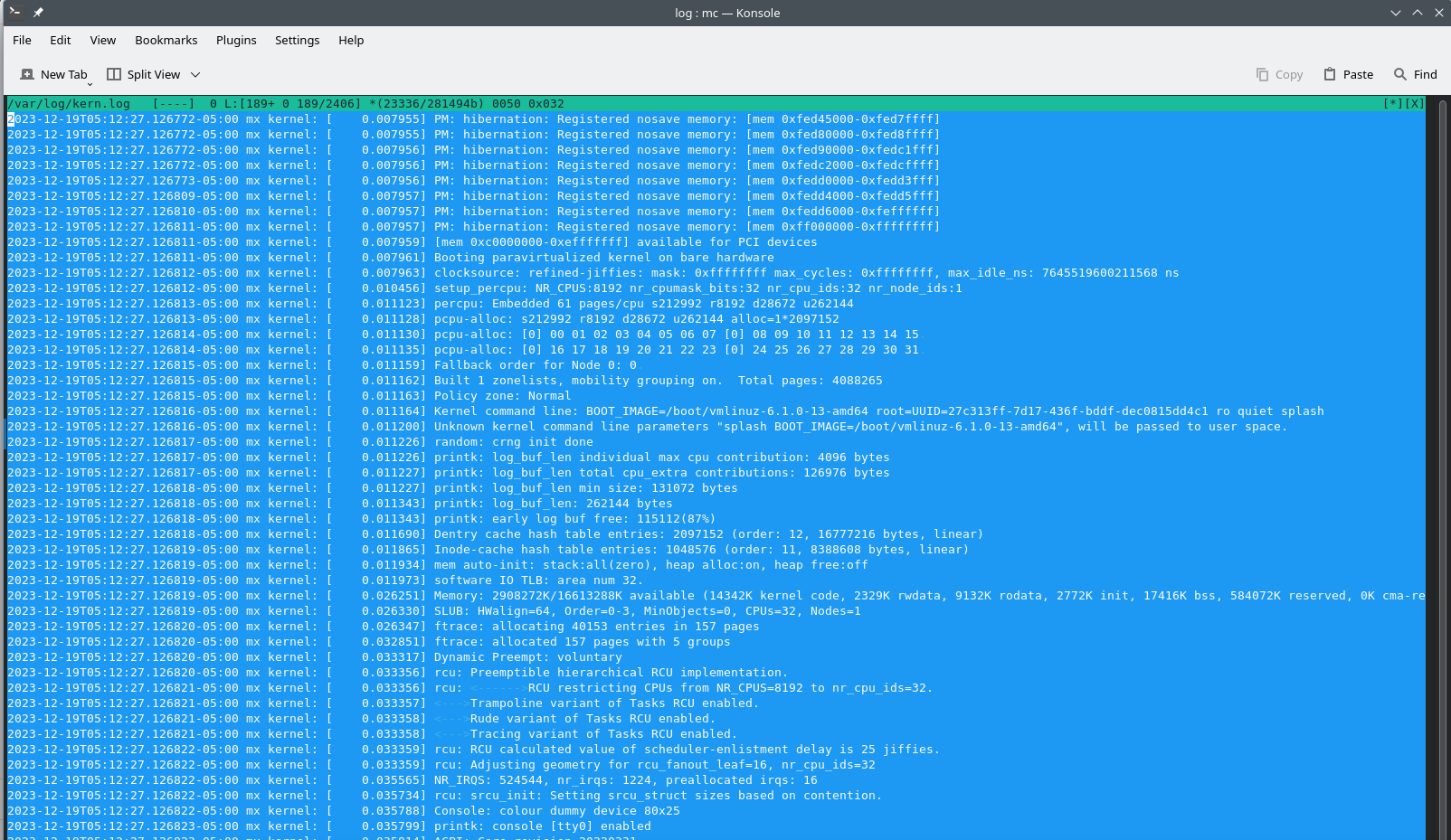
The company sent me to LinuxWorld in San Francisco, all expenses paid and I took the LPI exam. The only issue was they wanted dpkg and I was source, aptitude and midnight commander. Sure, as a dev, now I have all the commands, but I felt that was an unfair situation because I was top notch.
I wrote the chapters using man pages and testing only. There were no guides, references or anything of that nature.
Ultimately, they sunset this training at or about 2018. Yea. I found out from one of the college professors. About time. Haha. I don’t know how many people learned Linux because of this work, but I was glad to be a part of that.
The history section came straight from a conversation I had with RMS about the history as I had just finished my internship with FSF in 2003.
The other thing I wanted to mention about this was in the beginning, there were questions from the IT support person as to my skills. He nagged at the sys admin who hired me. One day when the other IT staff had left, Josh, brought me over to the computer and said he had a new sound card and it wasn’t working.
So, I said, well you have to set the module in XFree86config file. He was like well what do I put there. I said, I’m not sure of that module for that brand. You can just search for it online. He had a serious spaz and was screaming at me… like I didn’t know what I was doing.
Section "Device"
Identifier " "
# Nothing yet; we fill in these values later.
EndSection
Then, I remembered. I had only used that brand unsupported on Linux once. So, I tried it and it worked. He calmed down and was very nice to me after that. See, there is really no reason to have to go through this type of trial or testing. I knew my stuff. I wasn’t upset about it at the time or even after but I was a little concerned my skills were treated with doubts until I “proved myself”. However, I was satisfied he had the confidence in my skills and a story to report back to the “haters”.
http://www.aries.net/cte/it_linux.html
I wrote this… in 2003.
Because I was not informed about limitations for non compete, I had to stop training at the end of the contract and took other work, trying to stay on free software systems and make a living.